it works fine when you have the correct configuration , watch the screenshot

zypper remove package
will not work you got an error like this
In case ‘exmaple’ is not a typo it’s probably not a built-in command, but provided as a subcommand or plug-in (see ‘zypper help subcommand’).
In this case a specific package providing the subcommand needs to be installed first. Those packages are often named ‘zypper-exmaple’ or ‘zypper-exmaple’.
solution is
zypper remove -u package
In the good old days you are used ifdown and ifup and so you can bring up a network interface. Now you have systemd and you should use networkctl
networkctl list => show all interfaces
networkctl down eht0
shutdown interface
networkctl up eht0
bring up interface
https://manpages.ubuntu.com/manpages/kinetic/en/man1/networkctl.1.html
the last day I have this error very often on my old 6.7 VMware environment.
shutdown your vm, remove all network cards / nic => save
edit settins add new network cards /nic
dmidecode | grep--color -i serial
how to install manually
https://www.tecmint.com/install-apache-tomcat-on-debian-10/
but we want to compile itself and build a deb package
we need java and ant
apt-get install ant
Choose your version as source code https://github.com/apache/tomcat/tags in our example we use 9.0.64
extract the folder and you can run /usr/bin/ant in the extraced tomcat folder after a frew seconds you can find your compiled tomcat under the folder /output/build
apt build-dep tomcat9
dpkg-buildpackage -rfakeroot -b -uc -us
MariaDB and MySQL sometimes realy strange. The last time I had offen dumps between sql server versions. you must not use my pipe for compression this is optional.
mysqldump –events –routines –triggers –single-transaction –default-character-set=utf8mb4 –opt database.dump | gzip > database.sql.gz
If you are need some stresstest for your MySQL server you can use mysqslap. I offen use this command
mysqlslap --auto-generate-sql --concurrency=100 --iterations=200
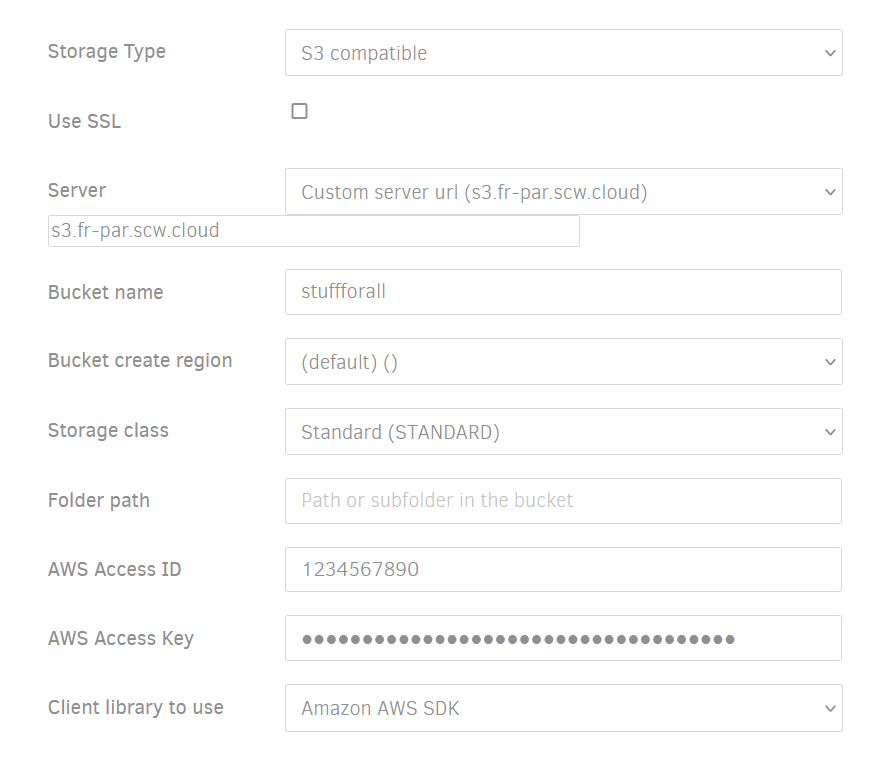
If you are searching for an alternative for Backblaze Backup. You can try rclone with s3 storage from Scaleway.
In these Blogpost you can find out how to install and configure it. But how to use it? I have some example for you.
https://www.scaleway.com/en/docs/tutorials/encrypt-s3-data-rclone/
https://www.scaleway.com/en/docs/storage/object/api-cli/installing-rclone/
Thats for a Windows machine, on Linux only other path K:test = /home/ubuntu/myfiles
rclone sync --progress K:\test Scaleway:allmybackup
If you want to store your data directly in to the GLACIER storage you can use
rclone sync --progress --s3-storage-class=GLACIER K:\test Scaleway:allmybackup
or you can configre rclone directly to use GLACIER directy without define storage class
Simple example if you are using encryption with rclone
rclone sync --progress K:\test crypt:
Now we have more options for bandwith usage
Attention rclone is using Megabyte not Megabit 1M are 8Mbit
rclone sync --progress --log-file=rclone_log.txt --bwlimit "06:00,2M 23:00,4M" K:\test crypt: